Healthcare Information Sharing Is Broken
An illustrative case study of how a Tier-1 Research Medical Center achieved Zero Trust application networks with HL7 FHIR APIs and defeated AI-driven attacks using Hopr's Lane7 Blueprints

An illustrative case study of how a Tier-1 Research Medical Center achieved Zero Trust application networks with HL7 FHIR APIs and defeated AI-driven attacks using Hopr's Lane7 Blueprints

In 2025, healthcare enterprises faced a devastating wave of cyber threats driven by compromised credentials and supply chain vulnerabilities. Hacking and IT incidents accounted for over 80% of all large healthcare data breaches, proving that legacy perimeter defenses and static keys are failing against modern attack vectors.
Hopr's Korvette-S™ WoSPs enable MediCore Health to secure its clinical application workloads, APIs, and Protected Health Information (PHI) without a loss of agility.
A MediCore Health provider initiates a patient data request through the clinical portal, triggering MediCore's application to make an API call to a third-party diagnostic affiliate to retrieve lab results.
The third-party diagnostic vendor receives the API call containing sensitive PHI and MediCore's static API key. It authenticates the key, processes the request, and replies to MediCore with the clinical data. No workload identity trust verification has occurred , and both messages are merely encrypted with conventional Transport Layer Security (TLS).
The MediCore application receives the third-party diagnostic data, processes it, and provides an update to the patient's Electronic Health Record (EHR), and provides an update to the patient portal, too. The processing requires several microservice API transactions internal to MediCore, operating across different clusters and cloud environments.
The MediCore EHR database and the patient's portal are updated after the transaction processing is complete. The patient and provider are unaware that vulnerabilities in the third-party API exchanges led to the compromise of sensitive PHI and that malicious actors now possess MediCore's API keys for unimpeded lateral movement.
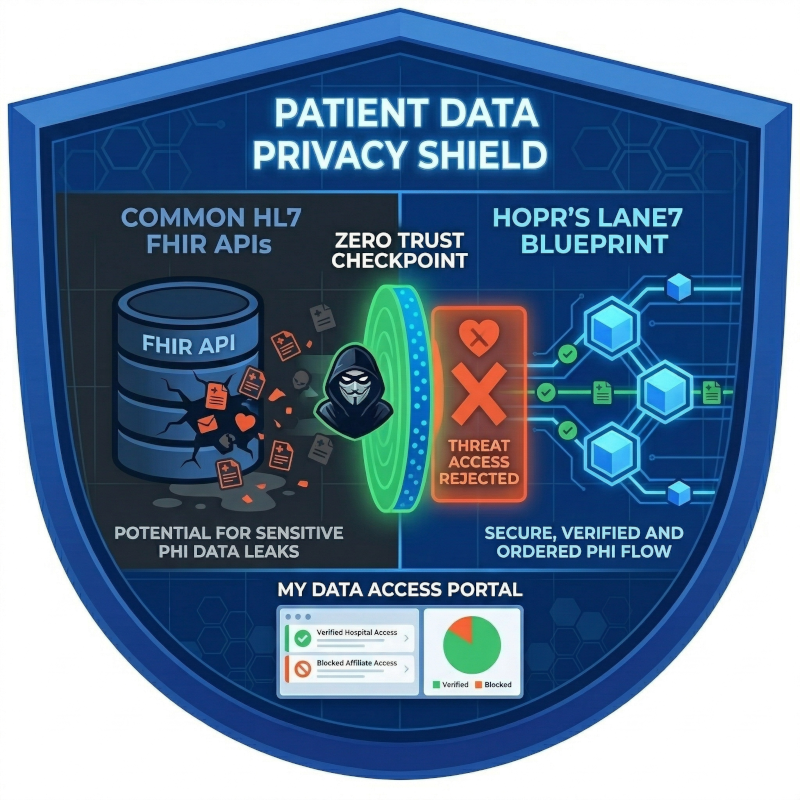
MediCore's business relied on sharing clinical data among affiliated partners through portals. They deployed a Zero Trust Application Network using a Lane7 Blueprint which was custom-composed for their clinical network. The Blueprint was quick and simple for each affiliate to deploy their Zero Trust app network and interconnect it among other clinical affiliates. Third-party security teams welcomed the additional Zero Trust assurance to their security architecture.
Korvette WoSPs, pre-configured in the blueprint, assured secure and trusted internal and edge API transactions.
MediCore's API protections could not verify identity trust and prevent abuse of stolen API keys.